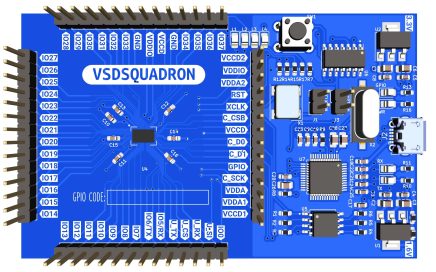
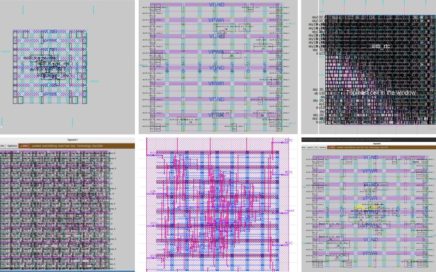
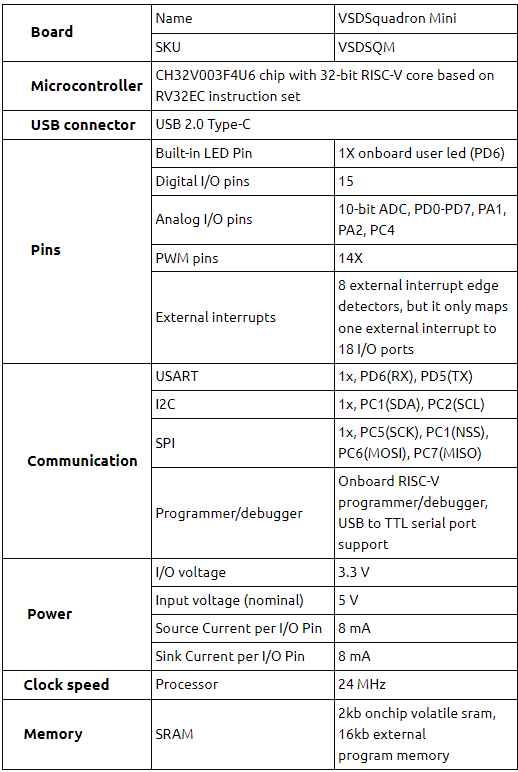
The VSDSquadron educational board provides a unique opportunity for learners to gain hands-on experience in electronics system design and chip design. The board’s open-source nature allows for easy access to IPs, PDKs, and tools, including RISC-V, providing learners with a complete and comprehensive curriculum in these areas. With the board’s built-in modules covering a range of topics such as analog IP design, RISC-V SoC design, PCB design, and more, learners can acquire practical skills and knowledge essential for a career in the field. In summary, the VSDSquadron educational board offers a rich and dynamic learning experience in electronics system design and chip design.
International payments are now open. You can pre-order your board using below link
https://www.vlsisystemdesign.com/vsdsquadron/