Implementing Moisture Sensor using VSDSquadron Mini
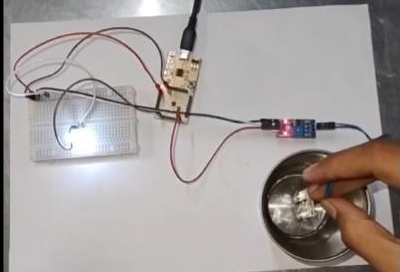
Overview The project demonstrates the implementation of a moisture sensor using the VSDSquadron Mini, a RISC-V based development kit. The core concept revolves around detecting […]
Overview The project demonstrates the implementation of a moisture sensor using the VSDSquadron Mini, a RISC-V based development kit. The core concept revolves around detecting […]
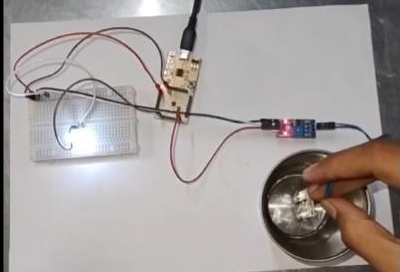
Overview The Smart Door project presents an innovative integration of infrared (IR) sensing technology with the CH32V003 RISC-V processor to create an automated door system. […]

Another Big Day for VSD and its community….
NASSCOM Positions VSD at the Forefront of VLSI Skilling Initiatives in India. Read blog for more details.
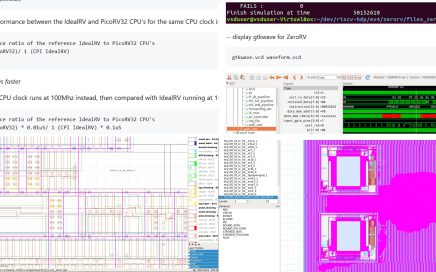
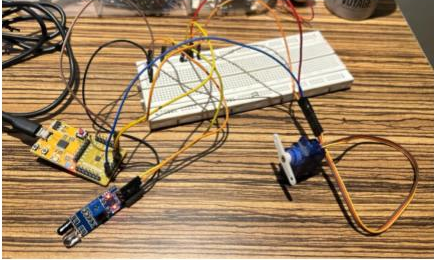
Look at these images from RISC-V HDP program conducted by a 14yr old company (VLSI System Design) VSD In the realm of learning and professional […]

Welcome to a milestone in the world of VLSI and semiconductors – the VSDOpen2023. This year’s conference is not just another event; it’s a defining moment that promises to reshape the contours of the industry.

India, the land of innovations and revolutions, is on the brink of another technological metamorphosis. And you, the young minds of our great nation, are […]
Read our interview at Electronics for you (EFY) magazine and dive into the transformative world of VLSI with the enlightening article that serves as a beacon for all aspiring electronics enthusiasts. VLSI, or Very Large Scale Integration, isn’t just a technical term; it’s a vision that beckons the future of electronics, breathing life into devices by embedding millions of transistors on a singular chip. This incredible feat of engineering has not only redefined the electronics landscape but has also expanded the horizons of what’s conceivable.

Working with real chips also provides an opportunity to develop problem-solving skills. You will encounter errors and glitches while working with the chips, and you will need to use your creativity and critical thinking skills to identify and solve the problems. This process helps to build a problem-solving mindset that is essential for success in the field of electronic design. In conclusion, the labs using real chips offered by “vsdsquadron” provide a unique learning experience that is essential for gaining a deep understanding of VLSI and RISC-V. It allows you to develop hands-on experience with the technology, build practical skills, and foster a problem-solving mindset.
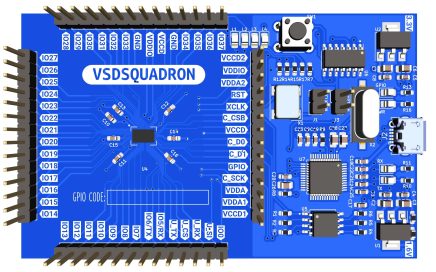
The VSDSquadron educational board provides a unique opportunity for learners to gain hands-on experience in electronics system design and chip design. The board’s open-source nature allows for easy access to IPs, PDKs, and tools, including RISC-V, providing learners with a complete and comprehensive curriculum in these areas. With the board’s built-in modules covering a range of topics such as analog IP design, RISC-V SoC design, PCB design, and more, learners can acquire practical skills and knowledge essential for a career in the field. In summary, the VSDSquadron educational board offers a rich and dynamic learning experience in electronics system design and chip design.
International payments are now open. You can pre-order your board using below link
https://www.vlsisystemdesign.com/vsdsquadron/

With “vsdsquadron” under safe and capable leadership, it’s now the perfect time to expand the reach of RISC-V and VLSI chip design education to even more regions throughout India. Let’s empower and equip even more learners with the skills and knowledge to excel in these exciting fields.