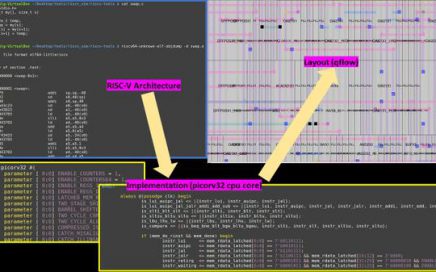
What can I do in 5-day VSD Workshop? Learn TL-Verilog and RISC-V
RISC-V and open-source hardware is undoubtedly destined to change the industry. Not just for the ISA and design, there are ongoing efforts to tape out an actual chip with completely open-source tools!
Join the revolution!